Hardcoded secrets remain one of the most persistent security failures in modern software development. API keys committed to Git, tokens…
From Claude Code Scan to Automated Secret Remediation: Building a Secure MCP Server for AI Agents
Hardcoded secrets remain one of the most persistent security failures in modern software development. API keys committed to Git, tokens…

Ingress has been the standard way to expose Kubernetes apps since 2015. It went GA in 2020 and gained huge…

This blog is primarily intended for cloud network engineers, cloud architects, cloud security engineers, security operations engineers, and platform engineers….

AI agents are no longer passive tools but are becoming trusted digital coworkers. They can fetch documents, schedule meetings, query…

Introduction At CyberArk, we’re always trying to find ways to make it easier for developers to securely manage secrets wherever…

Cloud Native computing moves fast and changes constantly. The Secure Production Identity Framework for Everyone (SPIFFE) has emerged as a…

In today’s fast-paced world of DevOps and cloud-native applications, managing secrets securely is critical. CyberArk Conjur, a trusted solution for…

This post has been updated for Istio version 1.11.4 A service mesh is an architectural pattern that provides common network…

This blog will walkthrough the setup of GKE Autoneg, along with creating all the resources you need e.g. Backends Health…

In this post, we’ll take a look at a new change to Workload Identity Federation on GKE that can reduce…

An Internal Kubernetes Platform is a bespoke service offered to employees of an organization that provides access to a Kubernetes…

TL;DR DNS-based GKE endpoints change how public and private control planes can be accessed externally and internally in Google Cloud…
Google provides several mechanisms to give workloads accessing Google Cloud (GCP) services an identity. This identity allows Google to authenticate…

Developer enablement is being accelerated and simplified through the adoption of internal development platforms (IDP) and the re-emergence of software…
Introduction Cyberattacks have become increasingly sophisticated, and attackers are constantly coming up with new methods to gain unauthorized access to…
Many developers were left wondering which secrets were compromised and what code needed to be updated after attackers breached CircleCI…
In DevOps, securing your software supply chain is paramount, ensuring that your applications are not compromised by malicious actors. That’s…
The bots are here…and they can code! AI tools like ChatGPT from OpenAI have burst onto the market and have…

Sold. Out. For the first time ever, KubeCon Europe 2023 was sold out (in a venue that can hold about…

If you are reading this, you probably got sucked into watching Game of Thrones when it first aired on HBO…

Conjur Open Source is a robust secrets management tool to manage, audit, and control access across multiple platforms. Let’s explore…
The Ansible Tower integration with CyberArk Conjur allows users and administrators to map sensitive credentials (like passwords, SSH private keys,…

Secrets management assists organizations in authenticating applications and checking clients before allowing them to access sensitive information, systems, and services….

No matter their occupation, nobody likes to do the same set of tasks repetitively — especially when automation is an…

Many organizations are now deploying their containerized applications in Kubernetes clusters to achieve highly available, automatically orchestrated solutions. Often, however,…
The Conjur OpenAPI is a language agnostic API description standard that allows for both human and machine users to investigate…

Red Hat OpenShift is a Kubernetes-based platform for container orchestration. OpenShift differentiates itself from Kubernetes through features such as tight…
By default, Kubernetes uses Base64 encoding to store information such as application credentials, keys, and certificates. Unfortunately, this Base64 encoding…
Knative is the de facto standard for running serverless workloads in Kubernetes. But what do you do when your Knative…
Businesses need to provide flexible access to services that scale efficiently while always protecting customer data. Technologies like microservices and…

In recent years, there is a trend toward so-called low-code and no-code platforms. While no-code platforms often appeal to businesses…

In today’s world of cloud environments, deployments often use infrastructure as code (IaC). IaC deployments use a domain-specific language (DSL)…

With technology becoming a central part of our daily lives, we need to keep information safe from an equally rapidly…

Cloud-native applications use resources available to them online, on a public cloud platform, or hosted on-premises. IT teams apply policies…
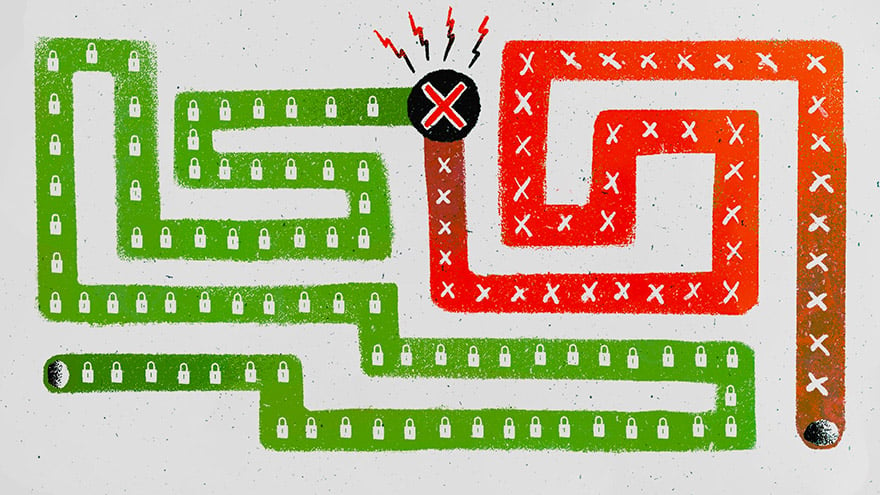
Most secrets management solutions rely on a master key or “secret zero” that can unlock other credentials. The problem is…

In the first and second articles of this series, we discussed managing the information needed to build and test applications….

The first article in this series discussed the value of integrating Conjur with Jenkins. This article focuses on implementing Conjur…
Handling secrets in cloud-native environments is a challenge for many organizations. Virtually any application requires some sort of secret, such…

Jenkins is a versatile platform for implementing continuous integration and continuous delivery (CI/CD) processes to develop applications. Using plugins, Jenkins…
Kubernetes is a popular choice for microservices because it provides scalable, portable, efficient deployment and reduces most DevOps overhead. Generally,…
While you are probably using IAM and CIAM at work and home, you might not know what they are or…
Managing cloud infrastructure isn’t a simple task at the best of times. From initial provisioning and configuration to maintenance and…
Secrets Management Policy Management through Java Spring Boot and Conjur The primary task of a secrets management administrator is to…
DevOps teams rely heavily on their CI/CD configuration tools to automate processes, accelerate delivery timelines and innovate at high velocity….

Organizations are migrating and deploying new workloads in cloud environments much more rapidly than ever, instead of expanding traditional on-premises…

We are thankful to have been a part of the four Kubernetes community filled days – five, including the day…

Ansible is an agentless management tool that can manage provisioning, configuration, and deployment of applications. RedHat acquired Ansible in 2015…
The Application Developer Access Dilemma As application developers, we need secure access to resources – such as databases, SSH servers,…

It’s not an overstatement that in today’s world, it’s dangerous to expose software services to the public without robust security…

Before the dotcom bubble bust in the early 2000’s, “irrational exuberance” drove stock valuations for internet companies that offered free…
2015 wasn’t very long ago, but when we look at significant events in computing, that was the year that the…
What is Terraform? Terraform is a tool for managing infrastructure as code. You define your architecture and software setup once,…
This integration allows Terraform users to leverage Conjur’s advanced non-human access control capabilities such as robust secrets management, tamper resistant…
Kubernetes permissions are built with role-based access controls (RBAC), which open up potential risks and need to be carefully controlled. …

I had the pleasure of recently eating dinner at Kitchen Market, a contemporary fusion restaurant in Tel Aviv’s port Namal….

I was really excited to attend the Cloud Native Computing Foundation’s (CNCF) KubeCon + CloudNativeCon Kubernetes conference in Seattle. I…

A Warning Sign Los Angeles is famous for its complicated parking signs: Sunny totems of rules and exceptions, and exceptions…

The last decade has been an exciting time for the tech industry, with the advent of collaborative business practices like…

CyberArk is incredibly pleased to announce the beta release of a new open source project, Secretless Broker. Secretless Broker makes…
CyberArk Conjur Open Source is now available as a Kubernetes application in the Google Cloud Platform (GCP) Marketplace. The new…

Fast software is satisfying to use, less costly to operate, and responds better to scale. Yet trying to improve the…
Buzz about Kubernetes is everywhere, and plenty of large organizations have adopted it. But what about smaller organizations? Is the…
Pulling at a loose thread One day I noticed an inconsistency as I was joining together lists of words. Consider…
Challenge Conjur is built to allow you to control access to your critical systems. This makes Conjur a critical security…

One of the biggest challenges in containerized environments like Kubernetes is the secure distribution of credentials and other secrets needed…

Martin Fowler’s popular article on microservices contains this advice: Going directly to a microservices architecture is risky, so consider building…

This is the sixth and final blog post in a series discussing how high-performing DevOps teams build secure systems at scale….

In the dynamic world of containers there are challenges around providing secrets needed for a containerized workflow without hurting the…
The Conjur team spends a lot of time thinking about security policies. We create them regularly for our own operations…
This is the fifth blog post in a series discussing how high-performing DevOps teams build secure systems at scale. If…

Configuring servers by hand is a costly and error-prone endeavor that increases in difficulty as the number of servers…

At their San Francisco Summit today, Amazon released AWS Secrets Manager. It’s a native AWS service that simplifies the…

If this article is the first time you’re hearing about CyberArk Conjur, you’ll probably want to read some of…

How would you assess your team’s current cyber security level within your organization? If you’re like most, your team…

Managing the SSH keys Ansible uses to connect to remote machines can be challenging. Placing keys on the Ansible…

This is the fourth blog post in a series discussing how high-performing DevOps teams build secure systems at scale….

We are excited to announce the release of a new integration between Conjur and Cloud Foundry (CF). Cloud Foundry users…

This is the first blog post in a series focusing on DevOps security workflows with Conjur. Check back for…

What happened at Tesla? Tesla’s Amazon cloud accounts were breached recently by hackers who put the stolen servers to…

Dr. Frankenstein’s monster is one of the most hated and misunderstood monsters of all time. Frankenstein brought his creation…

This is the third blog post in a series discussing how high-performing DevOps teams build secure systems at scale….

This is the second blog post in a series discussing how high-performing DevOps teams build secure systems at scale….

Even if you’ve never heard of Jenkins, you might be benefiting from it already: many companies and open source…

This is the first installment in a series of blog posts on this topic. Years have passed since the software…

Our Jenkins cluster had become a paralyzing mass of jobs, executor dependencies, and general complexity, not what you want…

We know it takes a lot to get a secure cloud automation project into production. Every day we are helping…