Introduction
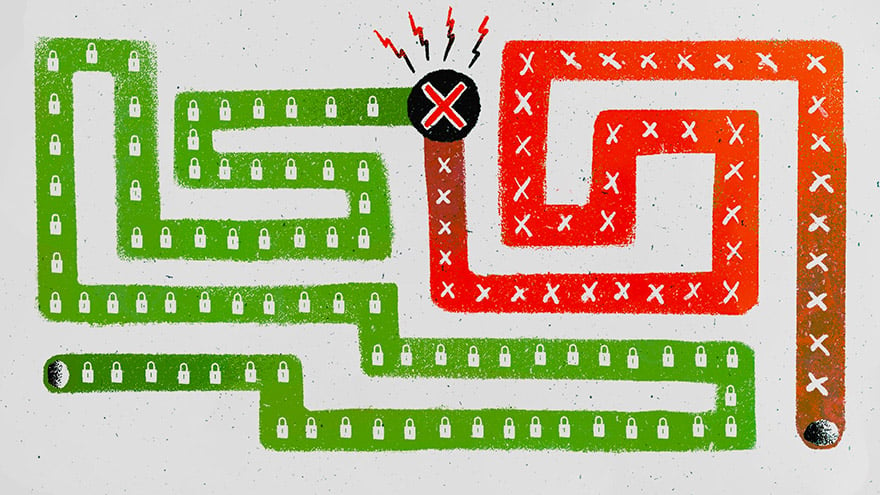
Cyberattacks have become increasingly sophisticated, and attackers are constantly coming up with new methods to gain unauthorized access to systems and steal sensitive information. One such technique that has gained traction in recent years is a poisoned pipeline. These types of attacks can threaten the build process of your CI/CD pipeline and wreak havoc on the software supply chain. Let’s take a look at what a poisoned pipeline is, some examples of high-profile attacks and how you can prevent attackers from poisoning your software pipeline.
What Is a Poisoned Pipeline?
A poisoned pipeline is a type of cyberattack where an attacker infiltrates a system’s software development pipeline, injecting malicious code or manipulating existing code to execute malicious activities during the build or deployment process. This allows the attacker to compromise the integrity and security of the software being developed or deployed, leading to devastating consequences. While we’ll get into some specific examples below, just think about the damage it could cause if you’re a software vendor for a large number of clients. By compromising your pipeline, the attacker could potentially gain access to your customers’ critical systems and data, causing massive damages, not to mention the reputational harm.
Poisoned pipeline attacks are particularly insidious because they can go undetected for long periods of time. Threat actors embed these types of attacks in the normal software development and deployment workflows. The malicious code can be disguised as legitimate code, making it difficult for traditional security measures to detect the attack.
Once the malicious code is executed, it can perform a wide range of activities, including stealing sensitive data, gaining unauthorized access to systems, spreading malware or disrupting critical operations.
There have been several high-profile cyberattacks in recent years that have utilized poisoning a pipeline as a primary attack vector. Let’s look at a few examples.
Docker Hub Compromise
In May 2018, Docker Hub, a popular containerization platform, announced that its database had been compromised, resulting in unauthorized access to sensitive data of millions of users. Further investigation revealed that the attackers had gained access to Docker Hub’s software development pipeline and injected malicious code into a publicly accessible component. This allowed the attackers to collect user credentials and gain unauthorized access to Docker Hub’s systems.
SolarWinds Supply Chain Attack
In December 2020, it was discovered that several organizations, including government agencies and Fortune 500 companies, had fallen victim to a massive cyberattack that originated through a supply chain compromise in SolarWinds’ software development pipeline.
The attackers inserted malicious code into an update for SolarWinds’ widely used Orion software, which was then distributed to customers as a legitimate update. The malicious code allowed the attackers to gain unauthorized access to the systems of the affected organizations and steal sensitive information.
Codecov Bash Uploader Compromise
In April 2021, it was revealed that the software development pipeline of Codecov, a popular code coverage tool, had been compromised. The attackers had gained access to Codecov’s Bash Uploader script and injected malicious code, which was then distributed to customers as part of their build process. The malicious code allowed the attackers to collect sensitive credentials and other data from the systems of Codecov’s customers.
These examples highlight the severity and complexity of poisoned pipeline attacks. They can have far-reaching consequences, compromising the security and integrity of software used by organizations and individuals alike. But if they’re disguised as legitimate code, how can you stop them from infecting your CI/CD pipelines?
How Can I Prevent a Poisoned Pipeline?
Preventing a poisoned pipeline attack requires a multi-layered approach. You should partner with your security team to ensure there are robust security measures at every stage of the software development and deployment pipeline, such as strong authentication mechanisms, code integrity verification and continuous monitoring for malicious activities.
When developing anun by CyberArk Labs, our team wanted to protect pipelines from cyberattacks – including poisoned pipeline attacks. So, we developed the Runtime Tracer. With this platform, users can track the full build process and be alerted of any suspicious activity. You can even automatically abort without causing chaos.
Conclusion
A poisoned pipeline attack is a sophisticated cyberattack technique that targets software development and deployment pipelines, allowing attackers to inject malicious code and compromise the integrity and security of the software being developed or deployed. As Docker Hub, Solar Winds and Codecov show, these types of cyberattacks can be damaging not only to your organization but also to any users of the infected software. Ensure your code is safe in the build process by partnering with your security teams on incorporating layered defenses into each stage of the software development lifecycle so that you can keep the poison out of your pipelines.

Einat is CyberArk Lab’s Innovation Product Manager. With a background in R&D, Einat not only keeps our product development on track, she also ensures that we continue to align our roadmaps with our customers’ highest priority needs.