If you are reading this, you probably got sucked into watching Game of Thrones when it first aired on HBO…
The Sword in the Darkness, the Watcher on the Wall


If you are reading this, you probably got sucked into watching Game of Thrones when it first aired on HBO…

Mainstream technology enterprises widely use Kubernetes. It’s an extendable, lightweight, open-source container orchestration platform. This popular platform has an ever-expanding…

Maintaining secrets in a secure way is an important — though often overlooked — aspect of security. DevOps security often…
DevOps teams rely heavily on their CI/CD configuration tools to automate processes, accelerate delivery timelines and innovate at high velocity….

Organizations are migrating and deploying new workloads in cloud environments much more rapidly than ever, instead of expanding traditional on-premises…
Learning is fun, and the best way to learn is through hands-on exercises. That’s why Conjur provides some tutorials to…

Conjur controls access to secrets using role-based access control (RBAC). We cover this in detail in Policy Concepts, but, to…

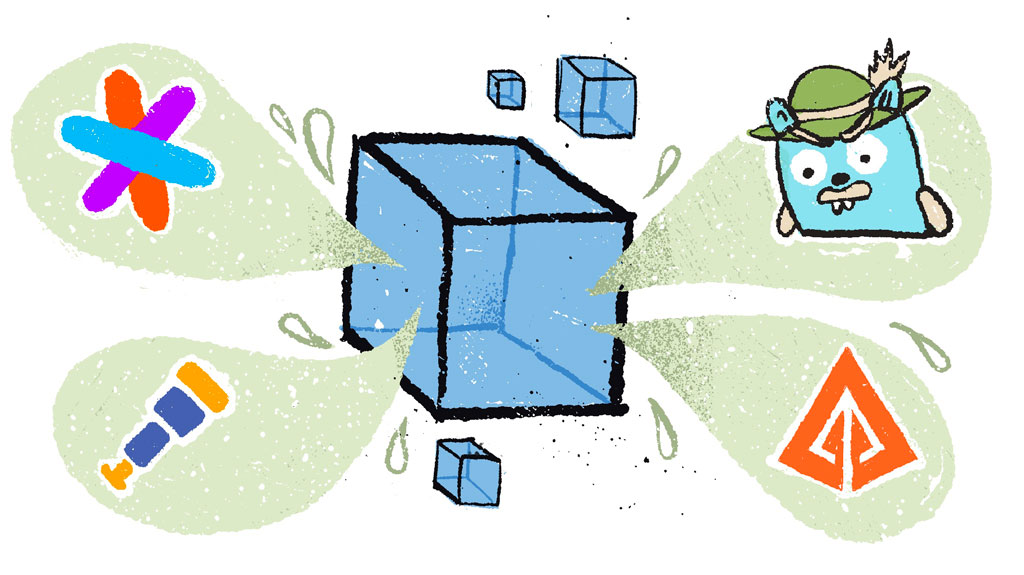
Since our first release of the Conjur Open Source Suite (OSS) aimed at helping development teams make the most of our secrets management…

Software and infrastructure architecture are quickly evolving into cloud environments. With this migration, Infrastructure as Code (IaC) is melding with…
One of the most important aspects of today’s cloud infrastructures is secrets management. There are many possible solutions, all of…
Visibility is a key requirement when working with containers and microservices, especially in complex environments where it’s hard to keep…

Chaos engineering, which aims to make software-based systems as resilient as possible in the face of unexpected error conditions, is…
Developing modern web applications in the cloud nowadays is more streamlined than ever. This is true because many external vendors…
Microservices are taking the world by storm, and the movement isn’t showing signs of slowing down any time soon. The…

Over the past decade, software development and information technology operations have become more integrated, spawning a new approach, commonly called…

We have talked a lot about the speed at which DevOps innovation has moved and how security has consistently struggled…
We all want our Open Source projects to be clear and simple to contribute to and we may think that…

Ansible is an agentless management tool that can manage provisioning, configuration, and deployment of applications. RedHat acquired Ansible in 2015…
This week we sent some of our team to DevOpsDays Boston. As usual, the real strength of the event were…

The SSH or Secure Shell protocol has become the industry standard for logging into one computer from another. Engineers use…

CyberArk was happy to be a part of Jenkins World, aka DevOps World, which took place this year in San…
This is an article about washing dishes. This is also an article about DevOps, but mostly it’s about washing dishes….
Over the past decade, my career has evolved from Development to DevOps and most recently to DevSecOps. DevSecOps is the result of organizations…
When talking about increasing development velocity for your teams, containers are at the forefront of the conversation on the new…

In this article, we’re going to talk about the problems surrounding authorization for your AWS account. We’ll define what those…

The DevOps culture shift and the move to continuous integration and deployment have required different tooling and utilities than previous…
Introduction KubeCon is the premiere conference for the Kubernetes and cloud-native communities. Every year it is held jointly with CloudNativeCon,…
What is Terraform? Terraform is a tool for managing infrastructure as code. You define your architecture and software setup once,…

The Internet of Things, or IoT, is what allows us to take the power of computing beyond desktops, servers, and…
Back when I first became a programmer, it was a common practice to include database credentials right in the code…
This integration allows Terraform users to leverage Conjur’s advanced non-human access control capabilities such as robust secrets management, tamper resistant…
Scrum Standups: A Refresher Engineers working in teams that use Scrum should be familiar with the format of a daily…

I was really excited to attend the Cloud Native Computing Foundation’s (CNCF) KubeCon + CloudNativeCon Kubernetes conference in Seattle. I…

Ansible is an excellent tool for automating procedures across multiple machines. To do this, it uses multiple SSH connections to…

At CyberArk, code reviews are a part of daily life. Getting input from peers is essential to maintaining high code…

If your organization has been successful since before containers were a thing, then you probably already have a mix of…

CyberArk is incredibly pleased to announce the beta release of a new open source project, Secretless Broker. Secretless Broker makes…
CyberArk Conjur Open Source is now available as a Kubernetes application in the Google Cloud Platform (GCP) Marketplace. The new…

The Secret Zero Problem I have talked to a number of security conscious professionals across a wide range of…

With the rise of Go, cross-compiling platform agnostic code has become more accessible than ever. Building a Windows binary of…
“The great thing about software and servers is they always work as expected.” – Said no one, ever When…

Containerization has taken the technology world by storm. Docker emerged as the de-facto leader in the base technology making it all possible. Because containerization necessitates consistency throughout your infrastructure, even…