When people hear the words “open-source project,” the image that often springs to mind is a very technical group of…
Security Best Practices for Cloud-native Development: A Review of Cloud Native Computing Foundation Resources
When people hear the words “open-source project,” the image that often springs to mind is a very technical group of…

If you are reading this, you probably got sucked into watching Game of Thrones when it first aired on HBO…

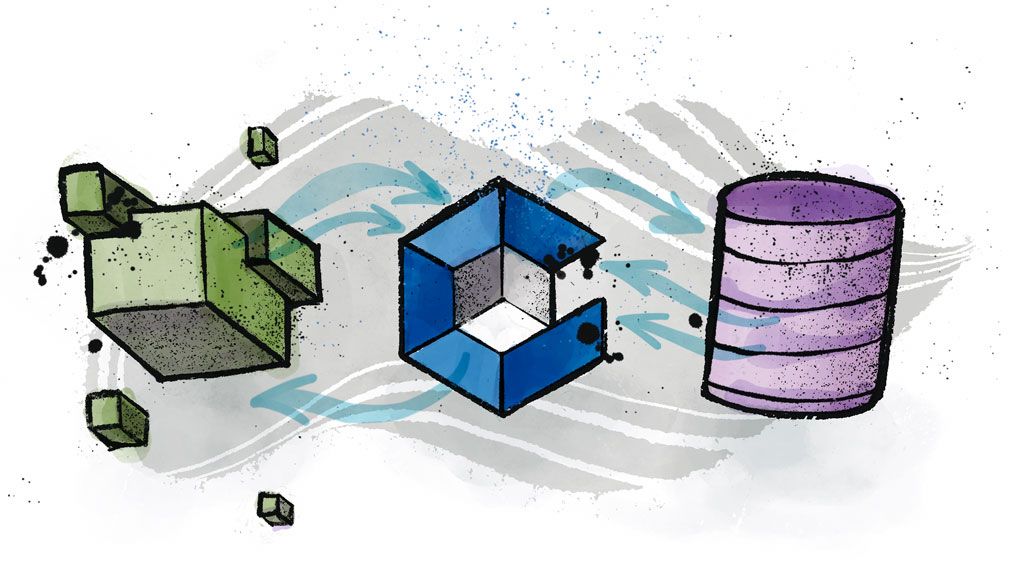
Conjur Open Source is a robust secrets management tool to manage, audit, and control access across multiple platforms. Let’s explore…
The Conjur OpenAPI is a language agnostic API description standard that allows for both human and machine users to investigate…

Red Hat OpenShift is a Kubernetes-based platform for container orchestration. OpenShift differentiates itself from Kubernetes through features such as tight…
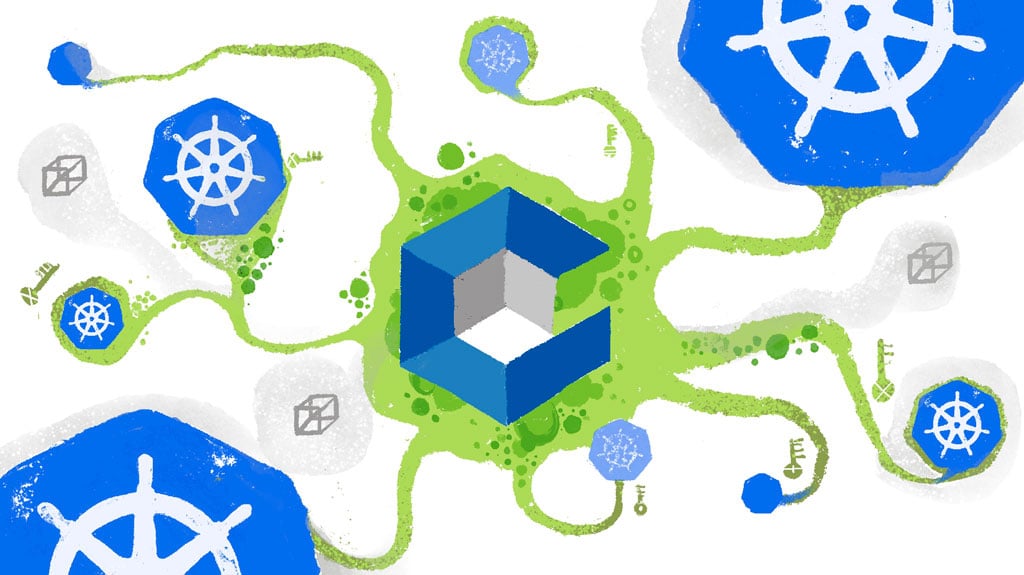
By default, Kubernetes uses Base64 encoding to store information such as application credentials, keys, and certificates. Unfortunately, this Base64 encoding…
Knative is the de facto standard for running serverless workloads in Kubernetes. But what do you do when your Knative…
Businesses need to provide flexible access to services that scale efficiently while always protecting customer data. Technologies like microservices and…

Mainstream technology enterprises widely use Kubernetes. It’s an extendable, lightweight, open-source container orchestration platform. This popular platform has an ever-expanding…

In recent years, there is a trend toward so-called low-code and no-code platforms. While no-code platforms often appeal to businesses…

In today’s world of cloud environments, deployments often use infrastructure as code (IaC). IaC deployments use a domain-specific language (DSL)…

With technology becoming a central part of our daily lives, we need to keep information safe from an equally rapidly…

Cloud-native applications use resources available to them online, on a public cloud platform, or hosted on-premises. IT teams apply policies…
Most secrets management solutions rely on a master key or “secret zero” that can unlock other credentials. The problem is…

In the first and second articles of this series, we discussed managing the information needed to build and test applications….
Handling secrets in cloud-native environments is a challenge for many organizations. Virtually any application requires some sort of secret, such…

Jenkins is a versatile platform for implementing continuous integration and continuous delivery (CI/CD) processes to develop applications. Using plugins, Jenkins…
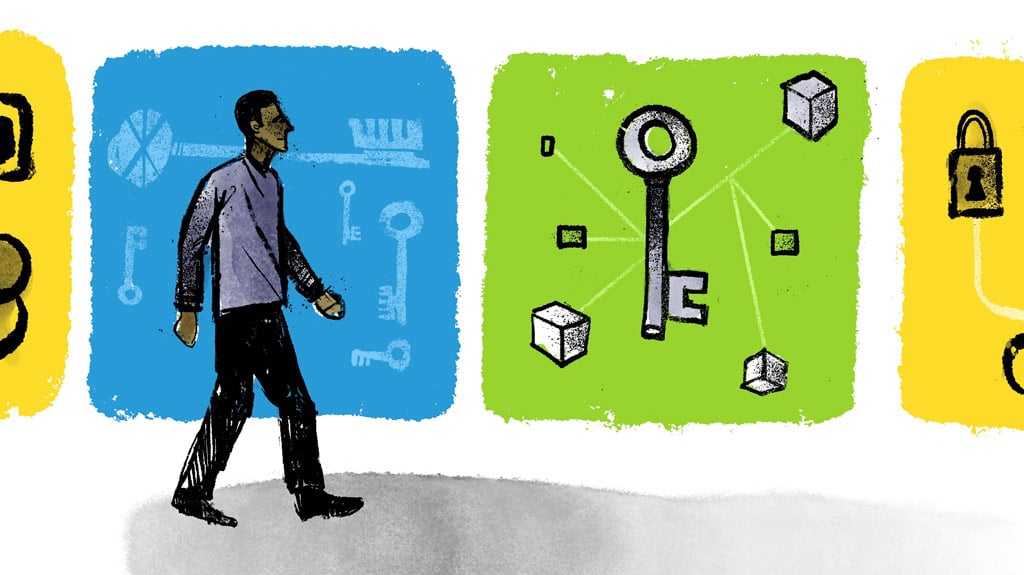
While you are probably using IAM and CIAM at work and home, you might not know what they are or…
Managing cloud infrastructure isn’t a simple task at the best of times. From initial provisioning and configuration to maintenance and…
Conjur provides excellent policy and command examples. The Getting Started with Conjur guides and Conjur Documentation should be your first…

Organizations are migrating and deploying new workloads in cloud environments much more rapidly than ever, instead of expanding traditional on-premises…

The recent SolarWinds breach prompted many organizations to take a hard look at their current cybersecurity practices, and get back…
Building a secure AWS environment requires applying security principles and guidelines around the way credentials and sensitive information are shared…

Conjur controls access to secrets using role-based access control (RBAC). We cover this in detail in Policy Concepts, but, to…

Software and infrastructure architecture are quickly evolving into cloud environments. With this migration, Infrastructure as Code (IaC) is melding with…
Kubernetes is a great orchestration tool for your containerized applications and Amazon’s Elastic Kubernetes Service (EKS) provides an easy way…
Once upon a time, access management was a simple thing. It focused mostly on making sure that the right users…
It’s not an exaggeration to say that enterprise ready machine identity frameworks are in greater need than before. This is…
One of the most important aspects of today’s cloud infrastructures is secrets management. There are many possible solutions, all of…

Applications often need to hold secrets. Connection strings, passwords, certificates, and other credentials are among the information applications may need…

Secrets management is a critical problem for developers, especially for teams adopting DevOps practices. Until recently, it was the IT…

When we talk about Secrets Management and handling secrets, we ought to think about all the users of the system…

Machine-to-machine communication is very important in today’s business-in-the-cloud. A lot of credentials and secrets are used and shared by non-human…
Some GitHub repositories don’t just contain code – they contain passwords, API tokens, and credentials. The worst part? These are…
Developing modern web applications in the cloud nowadays is more streamlined than ever. This is true because many external vendors…
Microservices are taking the world by storm, and the movement isn’t showing signs of slowing down any time soon. The…

Over the past decade, software development and information technology operations have become more integrated, spawning a new approach, commonly called…

We have talked a lot about the speed at which DevOps innovation has moved and how security has consistently struggled…

Ansible is an agentless management tool that can manage provisioning, configuration, and deployment of applications. RedHat acquired Ansible in 2015…
When you are developing an application, there are some important things that should not fall into the hands of strangers….

The SSH or Secure Shell protocol has become the industry standard for logging into one computer from another. Engineers use…

CyberArk was happy to be a part of Jenkins World, aka DevOps World, which took place this year in San…
Over the past decade, my career has evolved from Development to DevOps and most recently to DevSecOps. DevSecOps is the result of organizations…

In this article, we’re going to talk about the problems surrounding authorization for your AWS account. We’ll define what those…
Introduction KubeCon is the premiere conference for the Kubernetes and cloud-native communities. Every year it is held jointly with CloudNativeCon,…

The Internet of Things, or IoT, is what allows us to take the power of computing beyond desktops, servers, and…
Back when I first became a programmer, it was a common practice to include database credentials right in the code…
This integration allows Terraform users to leverage Conjur’s advanced non-human access control capabilities such as robust secrets management, tamper resistant…
Over the past few years, whether you’re a developer, a system administrator, or a security professional, your world has changed a…

I was really excited to attend the Cloud Native Computing Foundation’s (CNCF) KubeCon + CloudNativeCon Kubernetes conference in Seattle. I…

If your organization has been successful since before containers were a thing, then you probably already have a mix of…

CyberArk is incredibly pleased to announce the beta release of a new open source project, Secretless Broker. Secretless Broker makes…
CyberArk Conjur Open Source is now available as a Kubernetes application in the Google Cloud Platform (GCP) Marketplace. The new…

I’ve recently been working with secrets.yml files that point to different secrets for different environments, and I wanted to share…

The Secret Zero Problem I have talked to a number of security conscious professionals across a wide range of…

If you think you’re hearing about a company getting hacked almost every day, that’s because you’re correct: there were over…